How To Access Super Admin Privileges in Windows
5 min readWhether it’s for fun or productivity, accessing the Super Admin account on Windows has always been easy. Not because it’s not secure, but because Administrators often forgot what they were hired for: administering and securing the systems.
It’s yet easy to block a user from accessing Super Admin rights. Setting up tight rights for applications, files and folders is the ABC of the job. However, history has proven that it’s pretty rare that you couldn’t obtain these rights by a mean or another.
My goal was always the same: circumvent dumb company policy designed to prevented me from doing my job. Cannot change Windows Theme, colors, wallpaper, cannot install such and such tool… I’m a Linux system Admin and because of that I shouldn’t be a Windows Admin as well? What did you hire me for, dickhead?
On a more philosophical approach, it’s the lack of trust in employees that force companies to act that way. I understand it, since I recently took a class on Cyber Security Management. Threats can also come from the inside and therefore, employees cannot be given every privileges. However, a sweet balance should be met, for everyone’s benefit. Blocking users from modifying the theme is plain dumb.
What is Super Admin?
It’s important to make the difference between an Administrator account and the Super Admin account. There is no such Super Admin account to begin with. It’s just a shortcut name to explain that one can access an interactive console with System privileges.
Local System privileges is not an interactive user, it’s the core system user of Windows. Another one exists with a similar set of privileges, it’s called Network Service. Both are pseudo users with a set of ACL privileges that superseed any interactive user. It can access the Registry (SAM database) in read/write mode for instance, which is quite dangerous. Normally it’s used by services and system internal tasks only.
Example: an Administrator cannot even read the SAM database and registry files because they are locked:
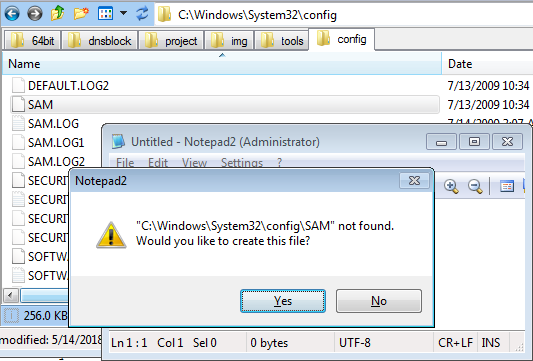
However you may want to backup them, for some purpose. Then you need the Super Admin privileges.
Administrator Privileges on Windows 3.x/9x/NT3.1
I think these systems just didn’t have any clue of what an ACL is.
Steal Administrator Privileges on Windows NT3.5/4.0
Things were slightly different at that time, and correct me if I’m wrong but Administrator user had all the rights needed to modify any part of the system. Thus, accessing a prompt with Admin privileges was sufficient if not the only way to gain Admin privileges to modify the system.
The trick of that era was so funny and easy I still LMAO. On Windows NT 3.5- 4.0, the screen savers were launched with Admin privileges, even for classic users. Since the Administrators of that era usually forbid users to change their screen saver, set by company policy (remember the dumb policies I mentioned), you couldn’t just copy CMD.exe to another file with an SCR extension and set it up as your screen saver.
The goal was then to simply replace the preset screen saver file at C:\Windows\System32\LOGON.SCR by a copy of CMD.exe. Since you cannot set another screen saver, just modify the current one in place! This actually worked every time because the ACL set for this file were often just not set. And I’m talking of Workstations that are part of a Domain!
Replace LOGON.SCR by a renamed copy of CMD.exe and start it, and Boom baby. Big security issue here.
Steal Super Admin Privileges on Windows XP/2000
That was another farce. The task scheduler was often left accessible to users, and the tasks were launched with Local System privileges. I’m talking about Workstations part of a Domain. Yes, yes. You know what to do!
The trick this time was to start a task at a certain time, say, one minute later, and launch a command prompt. So easy… Below is the script I used at that time:
set HH=%TIME:~0,2% set /A MM=%TIME:~3,2%+1 echo %HH%:%MM% at \\%COMPUTERNAME% %HH%:%MM% /INTERACTIVE "%SystemRoot%\system32\cmd.exe"
In cleartext, it give this:
HH=%TIME:~0,2%= current time in hoursMM=%TIME:~3,2%+1= current time in minutes + 1/INTERACTIVEmeans the user can interact with the process. Very important
And Boom baby, after less than a minute, a command prompt with Local System privileges appear. Big security issue here. To block this, just deactivate the Task scheduler service for users in the Domain Group Policy.
Super Admin Privileges on Windows VISTA
No clue since I never installed nor used it but I bet the previous trick or the ones for SEVEN would work on it.
Super Admin Privileges on Windows SEVEN
Ahaaa now we have a challenge. The task scheduler has been hardened and INTERACTIVE mode is disabled:
at \\DESKTOPNAME 10:58 /INTERACTIVE "C:\Windows\system32\cmd.exe"
Warning: Due to security enhancements, this task will run at the time
expected but maybe not interactively.
Use schtasks.exe utility if interactive task is required ('schtasks /?'
for details).
Added a new job with job ID = 2
The following tricks are accessible only for Administrators. Since XP, you cannot easily steal privileges anymore.
RunasSystem
Don’t worry. Before SP1, you could just become Local System Admin with a tool called RunasSystem.exe, available at SourceForge. You had to enable the trustedinstaller service first.
Here is a script to do just that automatically:
net start trustedinstaller if "%PROCESSOR_ARCHITECTURE%" == "AMD64" ( start RunasSystem64 ) else ( start RunasSystem )
PsTools
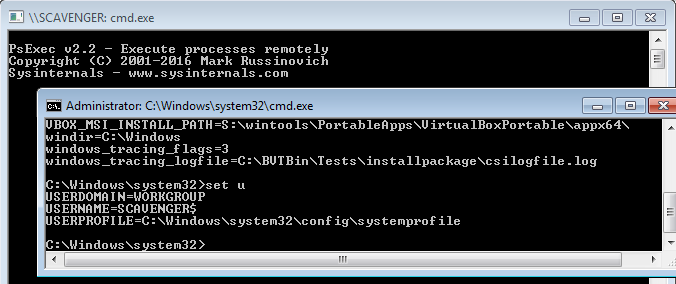
After SP1, or some obscure system updates it just didn’t work anymore. That’s fine, here is the new trick: psexec from PsTools by Sysinternals:
start psexec -i -s cmd.exe
And that’s it… As you can see, the new user for this Super Admin privileges prompt is “DESKTOPNAME$“:
Super Admin Privileges on Windows 8/8.1/10
Well, you can post your ideas here. I only use Windows 10 at school, and I haven’t been needing admin privileges just yet. Once, I needed to access certain system files, so I just rebooted on a flash drive loaded with Hiren’s Boot CD and started Mini XP. It’s pretty rare to see Bitlocker enabled on shared computers.
Still, accessing Super Admin privileges on windows 10 should be possible for Administrators. Has anyone tried the PsTools trick yet?